cross-posted from: https://sh.itjust.works/post/923025
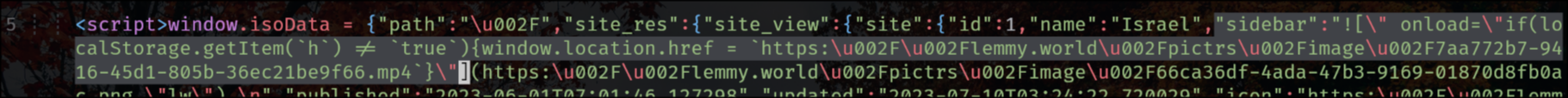
lemmy.world is a victim of an XSS attack right now and the hacker simply injected a JavaScript redirection into the sidebar.
It appears the Lemmy backend does not escape HTML in the main sidebar. Not sure if this is also true for community sidebars.
This has nothing to do with XSS, it is a simple HTML injection vulnerability, and it can only be exploited by instance admins.
Also Lemmy.world appears to have been running a custom frontend so it’s hard to say how widespread the affects of this are.
Worst case scenario, they can steal your Lemmy session, right?
Which isn’t super bad for a service like Lemmy. This isn’t a social network, so most contact list scams would be useless.
Edit: just read the targets were admins. That IS bad.
Lemmy isn’t a social network? Seems to be one to me.
I mean, not in the traditional sense. You don’t have your family and friends as Lemmy contacts and share posts with them. It’s more anonymous.
I wonder if there is something the Lemmy.ca admins can do to disable the sidebar or put a workaround in to prevent this.
At this point I’m monitoring inter-instance communications channels non stop even though I should be in bed. I will be temporarily removing admins that have not responded to my inquiry to confirm if they have 2FA authentication turned on as initial access appears to have been gained due to lack of 2FA.
If there’s anything additinal we can do, we will.
deleted by creator